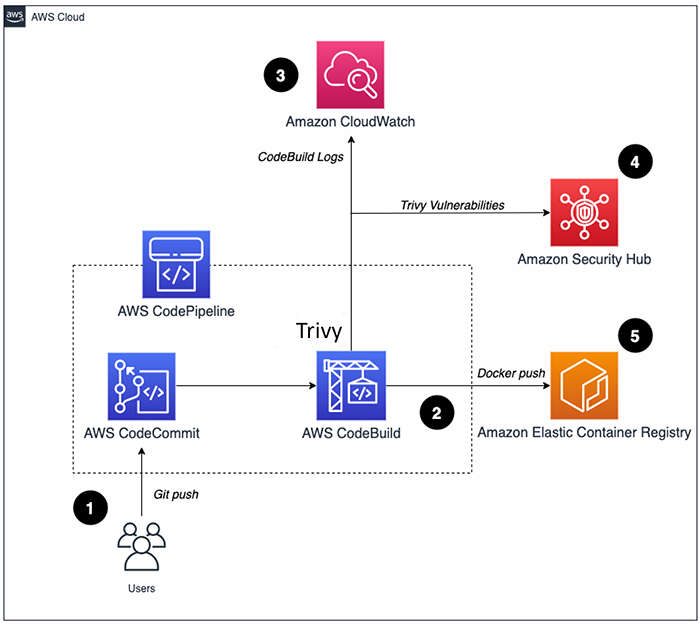
How to build a CI/CD pipeline for container vulnerability scanning with Trivy and AWS Security Hub | AWS Security Blog

Learn Wireshark: Confidently navigate the Wireshark interface and solve real-world networking problems: 9781789134506: Computer Science Books @ Amazon.com

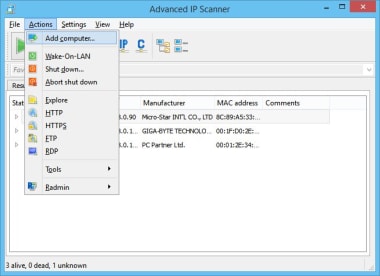
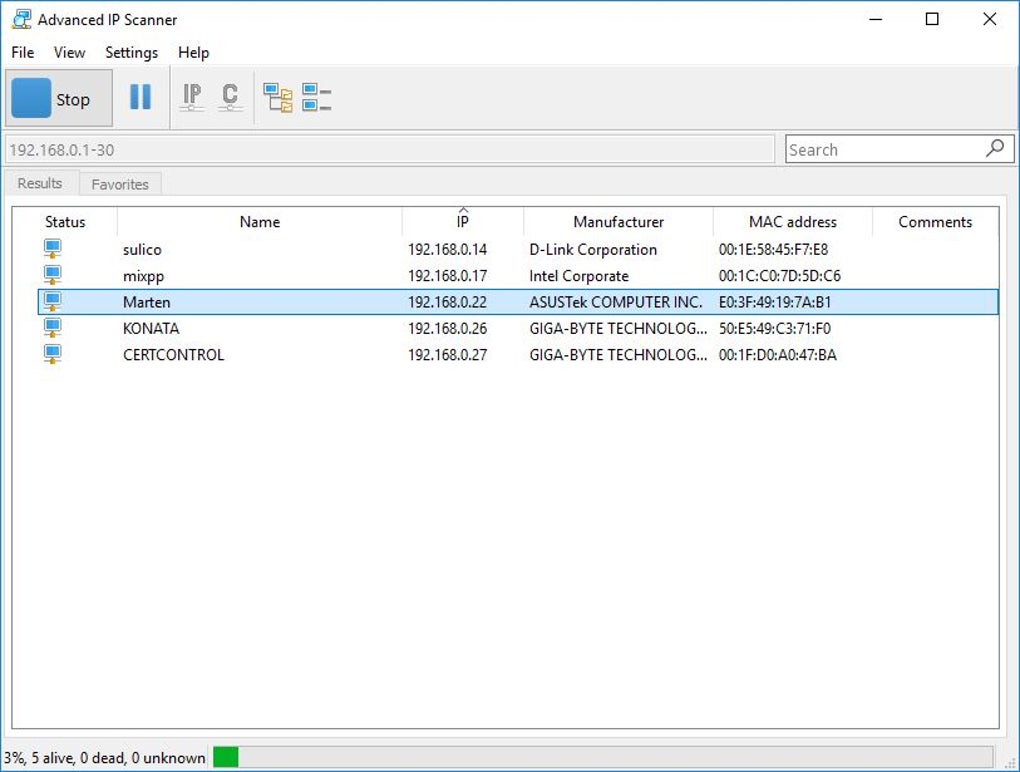
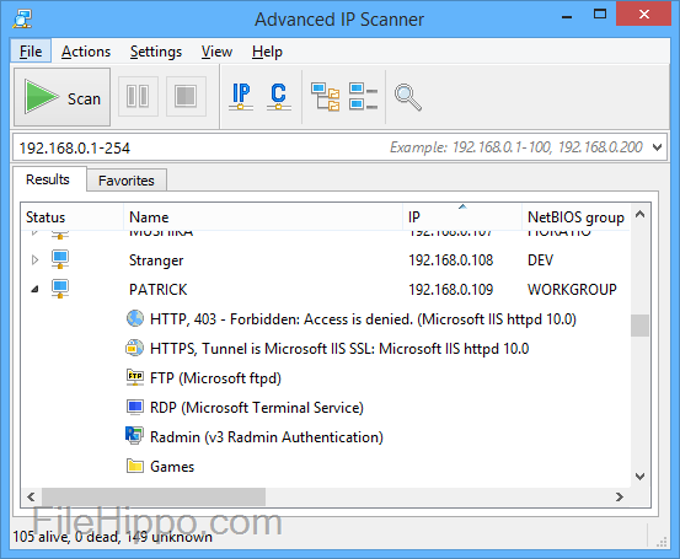
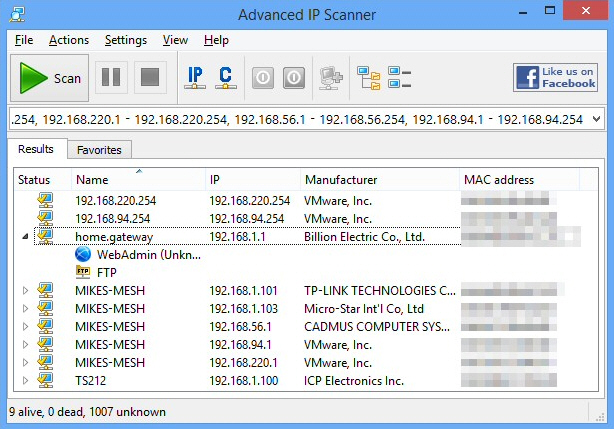
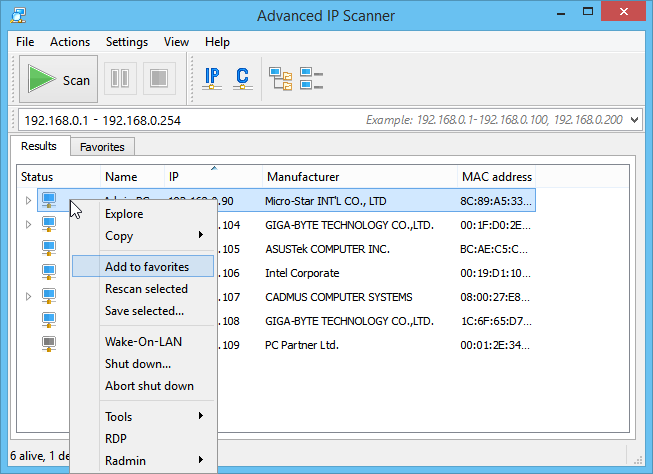
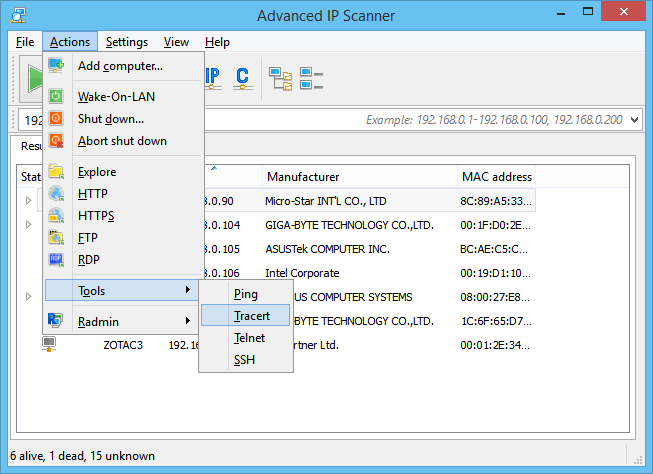
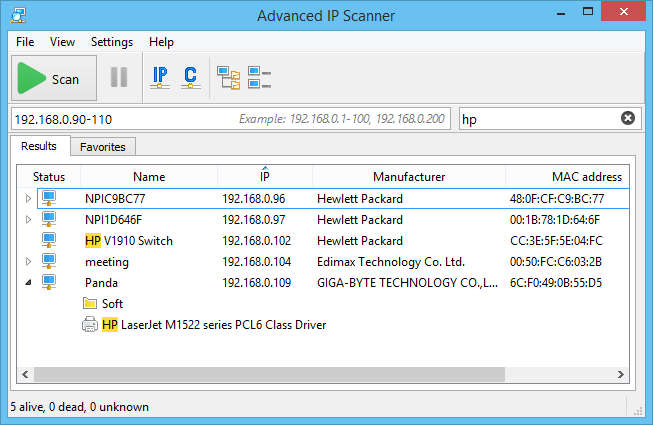
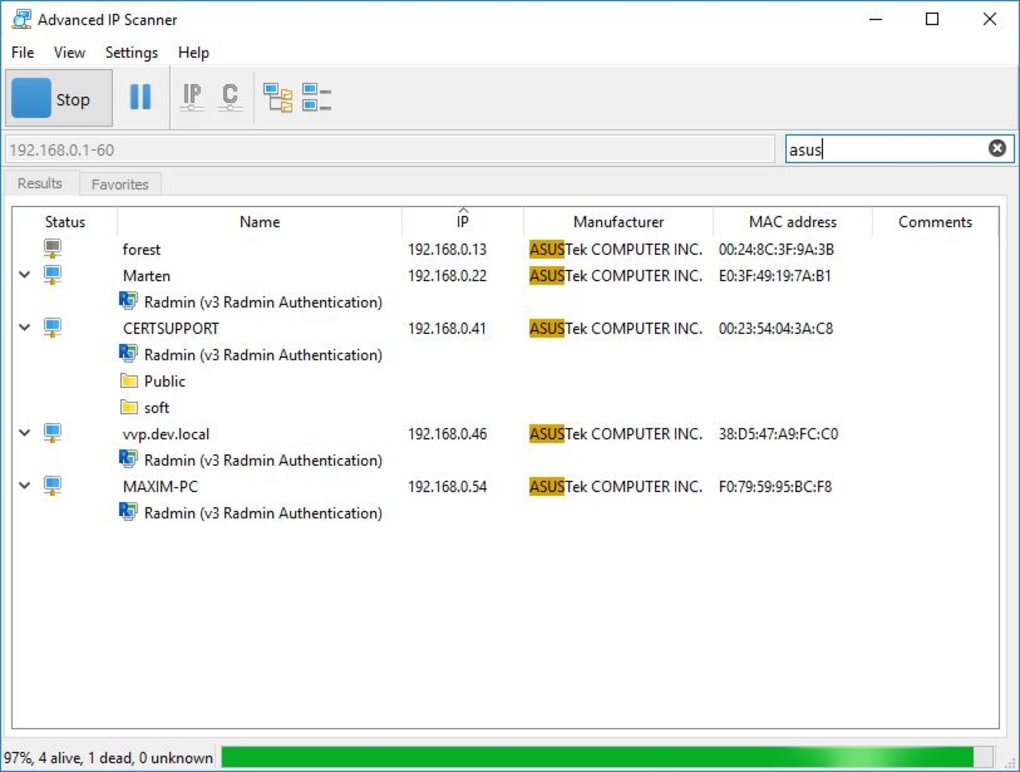
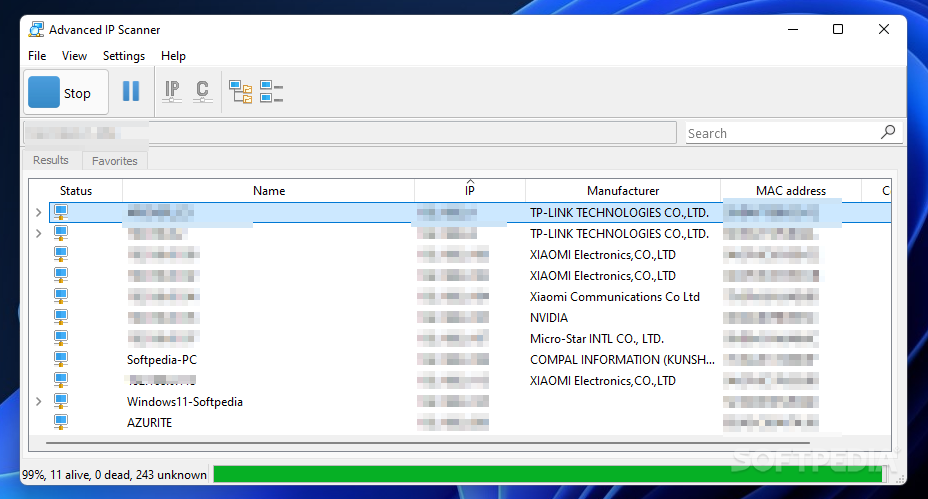
![What is Advanced IP Scanner and how to use it? [free download] What is Advanced IP Scanner and how to use it? [free download]](https://cdn.windowsreport.com/wp-content/uploads/2020/01/Advanced-IP-Scanner-main-window.jpg)